Wash Your Hands and Beware the Coronavirus Phishing Scam!
Day to day the media is reminding you to wash your hands and avoid large crowds as new coronavirus cases pop up across the world. What they should also be discussing is what else you should be concerned about; your cybersecurity. Global disasters such as the coronavirus creates a golden opportunity for fraudsters because the whole world is informed and constantly trying to learn more about said disaster. This causes a greater potential for impulse clicking on suspicious emails or attachments. The fraudsters know this. Starting in February 2020, a new coronavirus phishing scam has popped up in the United States. So, not only do you have to worry about the coronavirus outbreak hitting your area but now you must be on the lookout for the latest e-mail scam! These scam artists are trying to prey on the fear of the outbreak, hoping that you’ll impulse click on their seemingly legitimate e-mail and it’s working.
So how are these cybercriminals getting you to click on their e-mails and links? Scammers are sending e-mails pretending to be from the Centers for Disease Control and Prevention (CDC) or the World Health Organization (WHO) offering to provide an update on confirmed coronavirus cases in your area or luring you in with a link to see “safety measures” to combat the spread of the virus. Why do consumers believe these e-mails are real? One reason may be that the sender’s e-mail address at first glance could look very legitimate. The scammers create addresses that look very similar to the real organizations, making it very hard to catch. Another possible reason is that they also will copy and paste the organization’s logo in the e-mail to create a sense of legitimacy. Let’s look at a few examples of fake e-mails below.

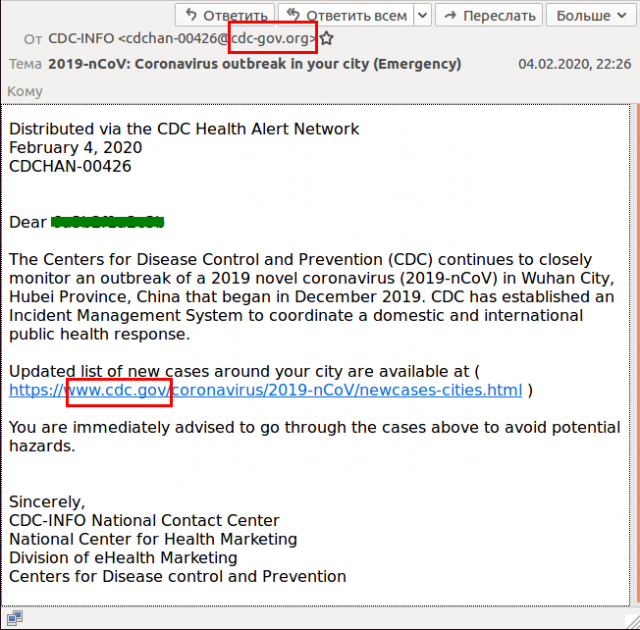
Sources: Image 1-Sophos Security Team, Image 2-Kaspersky
The above two e-mail examples are using classic phishing techniques to catch your attention. By using attention grabbing headlines and verbiage such as “EMERGENCY”, you are more likely to stop and read this e-mail. Once you click on the links embedded in the e-mail, you will be routed to a fake Microsoft Outlook webpage asking you for your e-mail login credentials. Once you submit your credentials, the hackers now have complete access to your e-mail. This means your contacts, messages, calendar, personal information, etc. Remember, your e-mail address is the login to many other websites which may include banking or investments. Let’s look at a different type of phishing technique below, this time asking for your donation.
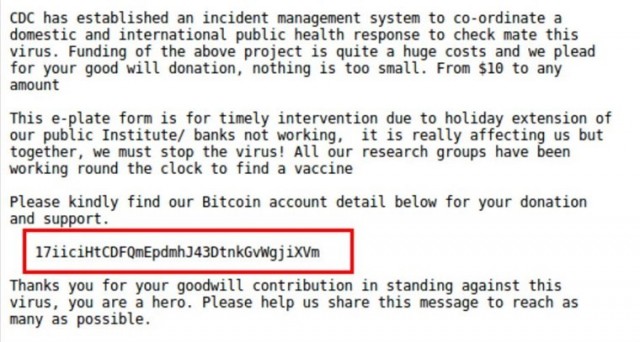
Image Source: Kaspersky
The above sample e-mail is trying to solicit your donation of bitcoin for an incident management system for the coronavirus. Once you donate bitcoin, the currency will not go towards combatting the coronavirus but instead go straight to a hacker’s untraceable account. Remember that the CDC is a government agency that is funded by U.S. tax dollars. It does not solicit for any donations and would especially not accept cryptocurrency.
Another popular phishing technique will ask you to open an (infected) attachment. Once you do this, your computer is immediately infected with ransomware and the hackers will demand a large amount of money in order to get your access back.
So, how do you spot a fraudulent coronavirus e-mail? Check out a few tips to spot red flags below:
-Look for spelling and grammatical errors.
-Look at the sender’s e-mail address.
-Don’t be convinced by the sender’s name, scammers can put any name they want in the “from” field.
-Be aware of an e-mail that is trying to create panic or requiring you to “act now” because of an emergency.
-Look for hyperlinks that do not direct you to a valid page.
*Check a link’s URL first before clicking it by copying and pasting it into your internet browser. Hyperlinks in e-mails can be directed to a different webpage upon clicking. Copying and pasting the URL first may prove the link they are telling you to click isn’t connected to a valid page.
How to protect yourself and what to do if you fell prey to a phishing e-mail.
1. Be Skeptical!
You should always be skeptical of any unsolicited e-mails, especially if it asks you to click on a link or open an attachment. Do not click on anything until you verify that the sender and e-mail attachments are legitimate. Contact the sender directly to verify if you are unsure.
Before you click on anything or enter your personal information, stop and think. Think about why the website is asking you for sensitive information. You should never enter personal data that a website shouldn’t be looking for. In this example, any site that is open to the public (like the CDC), will never ask for login credentials.
You shouldn’t panic if you accidentally provided sensitive information to the scammers. First, you should change all your passwords to any online accounts, including your e-mail. Setting up two-factor authentication (if applicable) on these online accounts is another great way to combat cyber fraud. This way even if the scammer has your login credentials, they cannot access the sites without having your authentication device (usually a cellphone).
If you opened up an infected attachment and lost access to your data; you should contact an IT professional to assist in recovering any data they are able to. Do not pay the hackers. For a proactive approach, I would recommend creating backups of important data stored on your computer on a somewhat frequent basis. This will make it much easier to restore access to your data in the event of a malware/ransomware attack.
In conclusion, you should be very aware of e-mail phishing scams at all times, not just during a crisis. It is very important to think before you open a suspicious e-mail or download any attachments. I hope this information aids you in avoiding any cyber fraud or e-mail scam in the future.
P.S. Don’t forget to wash your hands!
Commentary Disclosures:
The information contained in this commentary has been compiled by Covington Investment Advisors, Inc. from sources believed to be reliable, but no representation or warranty, express or implied, is made by Covington Investment Advisors, Inc., its affiliates or any other person as to its accuracy, completeness or correctness.
Under no circumstance is the information contained within this correspondence to be used or considered as an offer to buy or sell or a solicitation of an offer to buy or sell any particular security. Nothing in this correspondence constitutes legal, accounting, or tax advice or individually tailored investment advice, or research. This material is prepared for general circulation to clients, and does not have regard to the particular circumstances or needs of any specific person who may read it. The recipient of this correspondence must make his or her own independent investment decisions regarding any securities or financial instruments mentioned herein. Past performance is not indicative of future results.
To the full extent permitted by law neither Covington Investment Advisors, Inc. nor any of its affiliates, nor any other person, accepts any liability whatsoever for any direct, indirect or consequential loss arising from any use of this market commentary or the information contained herein. This correspondence may not be reproduced, forwarded or copied by any means without the prior consent of Covington Investment Advisors, Inc.
Investors should review this correspondence knowing that any comments and opinions made in this correspondence are subject to change and positions held by the authors may be sold.



